507 字
3 分钟
HGAME 2025 WP
W3ight#00005f-WEEK1-WP
MISC
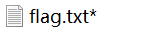
Hakuya Want A Girl Friend
观察.txt文件,发现打头为 50 4B 03 04 ,直接写脚本提取zip
def hex_to_zip(input_file, output_file): with open(input_file, 'r') as infile: hex_data = infile.read().replace('\n', '').replace(' ', '') binary_data = bytes.fromhex(hex_data)
with open(output_file, 'wb') as outfile: outfile.write(binary_data)
input_file = 'hky.txt'output_file = 'output.zip'hex_to_zip(input_file, output_file)压缩包内得到一加密txt文件
简单尝试爆破密码无果,回到hky.txt寻找线索
在文件最后发现 47 4E 50 89 ,判断应该讲PNG文件藏入并进行倒置
ctrl+f 查找倒置文件尾 82 60 42 AE
提取PNG文件部分,使用脚本倒置并生成PNG文件
def reverse_numbers_from_file(input_file, output_file): with open(input_file, 'r') as infile: lines = infile.readlines() reversed_lines = [] for line in lines: reversed_line = ' '.join(line.split()[::-1]) reversed_lines.append(reversed_line)
with open(output_file, 'w') as outfile: for reversed_line in reversed_lines: outfile.write(reversed_line + '\n')
input_file = 'hky.txt'output_file = 'output.txt'reverse_numbers_from_file(input_file, output_file)def hex_to_png(input_file, output_file): with open(input_file, 'r') as infile: hex_data = infile.read().replace('\n', '')
binary_data = bytes.fromhex(hex_data)
with open(output_file, 'wb') as outfile: outfile.write(binary_data)
input_file = 'output.txt'output_file = 'output.png'hex_to_png(input_file, output_file)同时进行宽高检测,最终得到图片

得到解压密码
flag:
Web
Level 24 Pacman
进入环境,吃豆人游戏
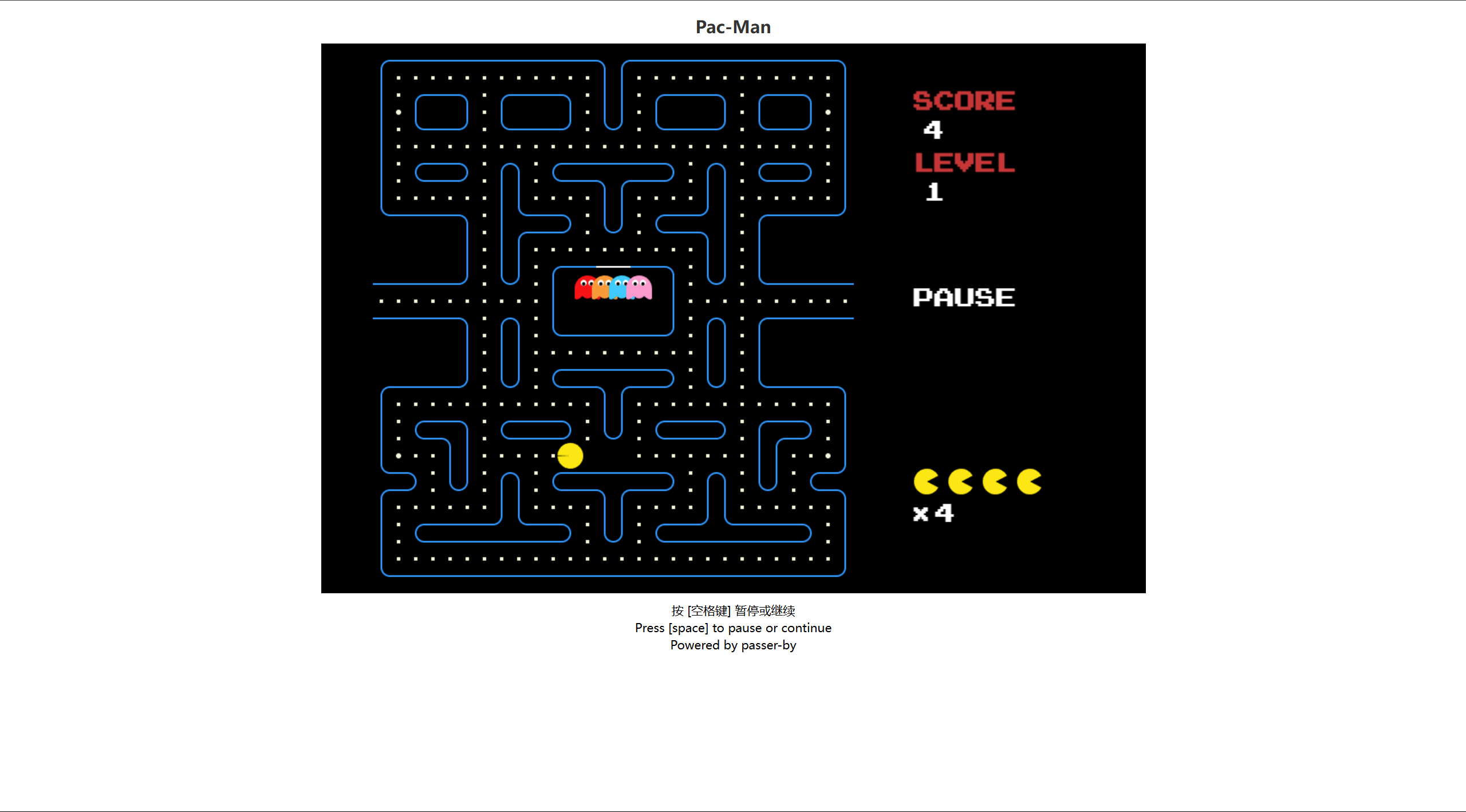
查看源码,在index.js 开头发现了类似Base64加密的密文

解密,得 haepaiemkspretgm{rtc_ae_efc}
猜测还有一层加密,多次尝试后发现为篱笆密码
解密,得 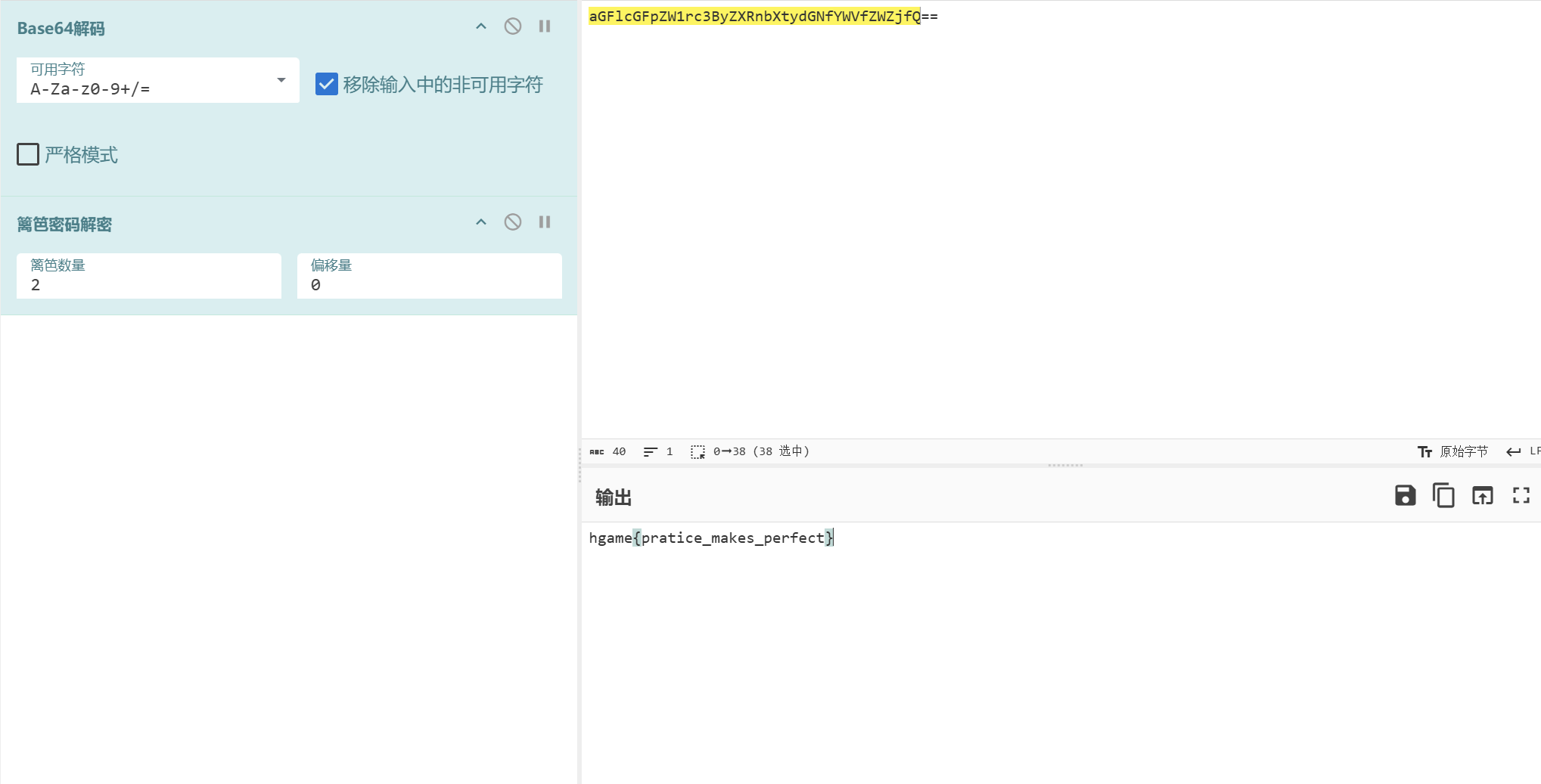
输入flag后发现不对,再次查看源码
又发现一串Base64密文
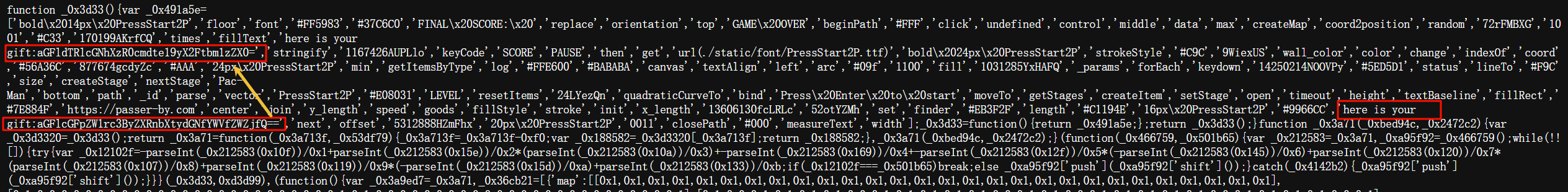
同上进行解密,得到flag: hgame{u_4re_pacman_m4ster}
Re
Compress dot new
打开附件,源码如下: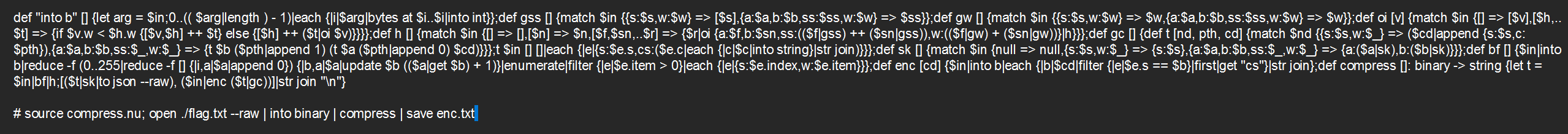
分析后发现程序对明文使用霍夫曼编码表对进行了编码
根据附件给出的enc和程序,解析霍夫曼树
“
import json
def parse_huffman_tree(data): if 's' in data: return {'s': data['s']} elif 'a' in data and 'b' in data: return {'a': parse_huffman_tree(data['a']), 'b': parse_huffman_tree(data['b'])} else: raise ValueError("Invalid Huffman tree structure")
def decode_huffman(binary_str, huffman_tree): decoded_data = [] current_node = huffman_tree for bit in binary_str: if bit == '0': current_node = current_node['a'] elif bit == '1': current_node = current_node['b'] else: raise ValueError("Invalid bit in binary string")
if 's' in current_node: decoded_data.append(current_node['s']) current_node = huffman_tree return decoded_data
with open('enc.txt', 'r') as file: lines = file.readlines() huffman_tree_json = lines[0].strip() binary_data = lines[1].strip()
huffman_tree = parse_huffman_tree(json.loads(huffman_tree_json))
decoded_bytes = decode_huffman(binary_data, huffman_tree)
flag = ''.join(chr(byte) for byte in decoded_bytes)print("Flag:", flag)得到flag:Flag: hgame{Nu-Shell-scr1pts-ar3-1nt3r3st1ng-t0-wr1te-&-use!}
HGAME 2025 WP
https://blog.lacrimosa.me/posts/hgame-2025/ 部分信息可能已经过时












